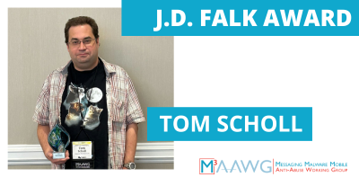
The Messaging Malware Mobile Anti-Abuse Working Group (M3AAWG) is proud to announce Tom Scholl as this year’s winner of the J.D. Falk Award.The award was presented at the 59th General Meeting, Oct. 9-12, 2023, in Brooklyn, N.Y.
Over the last few years, Scholl and others in the anti-abuse/distributed denial of service (DDoS) space have collaborated with many large and small networks across the globe to trace back Internet Protocol (IP) spoofed traffic to their sources and drive mitigation actions that disrupt the ability to generate these types of attacks.
Scholl is a Vice President and Distinguished Engineer at Amazon Web Services (AWS) in the infrastructure organization. His role includes working on AWS’s global network backbone, as well as focusing on denial-of-service detection and mitigation systems.
IP spoofing is a malicious attack that hides the true source of IP packets. The attacker changes the source IP address in packets to disguise themselves or impersonate another computer system. Attackers often use IP spoofing to launch denial of service attacks. These attacks attempt to overwhelm a target with traffic. With the identity of the attacker masked, it’s challenging to defend against them.
Over 20 years have passed since BCP38/RFC2827 proposed addressing the use of IP spoofing in denial-of-service attacks by recommending that networks implement anti-spoofing controls.
Spoofing is still present on the internet from some networks today because BCP38/anti-spoofing controls aren’t always implemented in networks.
Many broadband access networks have successfully deployed BCP38/anti-spoofing controls at the customer-facing edge over the years, thanks to outreach from individuals in the networking and abuse community. Unfortunately, these controls are not always enforced in the hosting provider space.
Upstream network providers can enforce mechanisms on their downstream hosting customers; however, this can present challenges as it relates to technical limitations on network equipment and the complexities of dealing with multi-homed downstream customers.
There are several motivations behind spoofing. Some people use it to bypass TCP/25 filtering to send spam, but one of the most popular use cases has been for launching distributed denial of service (DDoS) attacks.
DDoS-as-a-service providers, also known as booters or stressers, offer Layer 4 (L4) attack methods that take advantage of the ability to generate spoofed source IPs to launch attacks.
These attacks may be direct unicast floods of spoofed source IPs straight to the victim but are more commonly used in reflection/amplification attacks to generate large amounts of traffic toward a target.
While a target will observe traffic coming from reflectors, they generally cannot identify and trace back the true source that’s generating the spoofed traffic.
At the North American Network Operators’ Group 76th Gathering in June of 2019 (NANOG76) a practical solution was proposed to the spoofing problem with DDoS by identifying the pre-amplification/reflection traffic before it reaches the reflectors and tracing that back to the source network.
Scholl’s work to trace back the spoofed traffic to their sources includes educating network operators to become proficient in the ability to identify spoofed traffic and build abuse-related workflows to drive remediation here.
This is not an easy task, as it involves working with both large and small IP transit and hosting providers across the internet to identify sources and drive mitigations.
These engagements require providing examples of specific traffic flows observed, in addition to offering general guidance for how they can best self-identify this traffic on their own and streamline their customer engagement workflows.
The process may also involve developing other creative methods to identify and triangulate where spoofing is originating to explain to external networks which specific customers they should focus on when they struggle with identifying the specific customer.
Scholl and others in the anti-abuse/DDoS space will continue their work to trace back and suppress source IP spoofing as long as DDoS-as-a-service providers keep using this method.
Each year, M3AAWG’s leadership honors the legacy and spirit of J.D. Falk, by recognizing the work of an individual or team striving to improve end users’ online experiences and security. Scholl has worked extremely hard in tracing back spoofed traffic and mentoring the community of network operators and is most deserving of this award.
More than 50 sessions from experts fighting online abuse took place at M3AAWG’s 59th General Meeting in Brooklyn. You can find an overview here.



