Members Worldwide Gather at 55th General Meeting of the Messaging, Malware and Mobile Anti-Abuse Working Group (M3AAWG) in London to Address Current and Emerging Issues in Messaging, Malware and Cybersecurity
SAN FRANCISCO, Calif., May 27 – Members of the Messaging, Malware and Mobile Anti-Abuse Working Group (M3AAWG) will gather June 13-16, 2022 in London as part of its global collaboration on messaging and online abuse.
At its 55th general meeting, members and invited experts will address a number of topics related to its cybersecurity focus areas, including readiness, data and identity protection, communications and the supply chain. Sessions will include consideration of European Union (EU) and regional regulations and policies.
Dr. Victoria Baines, research fellow, Bournemouth University, will offer a keynote on predicting the future in cybercrime. She will discuss how to identify potential future developments in cybercrime by considering how technologies in development now might be used and misused in years to come. Dr. Baines will introduce how emerging technologies including artificial intelligence (AI), 6G, the Internet of Things, augmented reality, 4D printing and others might converge, along with their vulnerabilities and opportunities for misuse.
Baines previously was trust and safety manager for Europe, Middle East and Africa at Facebook. Previously, she led the strategy & prevention team at Europol’s European Cybercrime Centre (EC3) and was principal analyst at the UK Child Exploitation and Online Protection (CEOP) Centre. She began her career in law enforcement as a higher intelligence analyst for Surrey Police and is a member of the Advisory Board for the International Association of Internet Hotlines (INHOPE). She is a graduate of Trinity College, Oxford and holds a PhD from Nottingham University.
Meeting sessions will highlight prevention of brand phishing, email deliverability in the EU, technical operations, security controls, sender expectations related to AMP (accelerated mobile page) 4 email, cyberinsurance, email authentication and penetration testing. A training session will address verification of the various subjects when onboarding, performing additional due diligence, or investigating the abuse. Other sessions will examine DNS and DNSSEC, DKIM replay attacks and related topics.
More information and member registration can be found at /upcoming-meetings and Twitter (@M3AAWG), LinkedIn, Facebook and YouTube. Session updates and more info also will be posted on the blog.
About M3AAWG
The Messaging, Malware and Mobile Anti-Abuse Working Group (M3AAWG) is where the industry comes together to work against bots, malware, spam, viruses, denial-of-service attacks and other online exploitation. M3AAWG (www.m3aawg.org) members represent more than one billion mailboxes from some of the largest network operators worldwide. It leverages the depth and experience of its global membership to tackle abuse on existing networks and new emerging services through technology, collaboration, and public policy. It also works to educate global policy makers on the technical and operational issues related to online abuse and messaging. Headquartered in San Francisco, Calif., M3AAWG is driven by market needs and supported by major network operators and messaging providers.
Contact: Anne Price
anne@M3AAWG.org
602-330-6495
Messaging, Malware and Mobile Anti-Abuse Working Group Announces Updated Organizational Priorities, Focus Areas and Initiatives as Online Abuse Evolves
SAN FRANCISCO, Calif., May 18 – Continuing its widely successful efforts to fight online abuse and enable a safer Internet experience since 2004, the Messaging, Malware and Mobile Anti-Abuse Working Group (M3AAWG) today announced plans to focus its work around four key industry topics, including readiness, data and identity protection, communications and supply chain, as it continues the development of the organization.
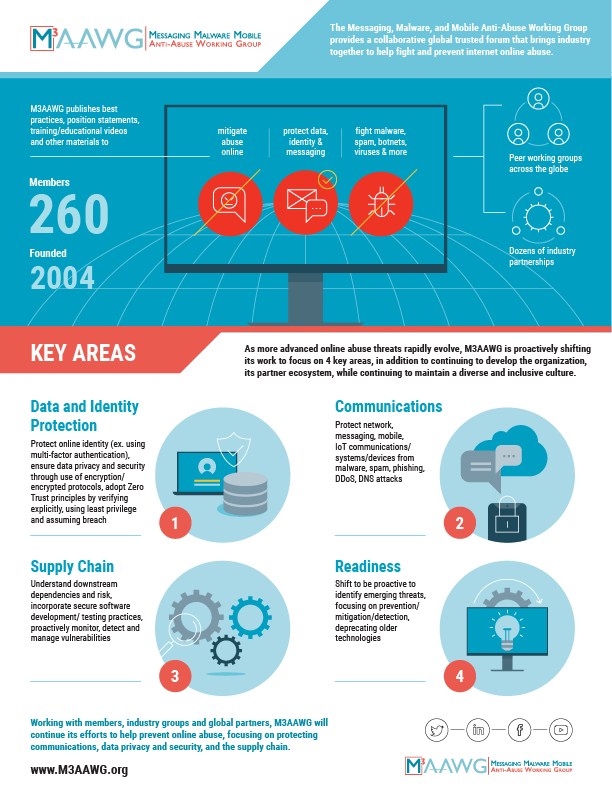
Based on today and tomorrow’s messaging, anti-abuse and cybersecurity environment, these focus areas will drive the efforts of M3AAWG’s committees, special interest groups and partnerships, while supporting the formation and development of new initiatives.
- Readiness: shift to be proactive to identify emerging threats, focus on prevention/mitigation/detection, deprecate older technologies
- Data and identity protection: protect online identity (ex. using multi-factor authentication), ensure data privacy and security through use of encryption/encrypted protocols, adopt zero trust principles that assume requests are breaches, must be verified explicitly and are using least privileges to help mitigate.
- Communications: protect network, messaging, mobile and IoT communications/systems/devices from malware, spam, phishing, DDoS and DNS attacks
- Supply chain: understand downstream dependencies and risk, incorporate secure software development/testing practices and proactively monitor, detect and manage vulnerabilities
- Organization: M3AAWG will continue its efforts to strengthen and build the organization, which is largely comprised of volunteers, via its diversity and inclusion efforts and global outreach and partner organizations
“For almost 20 years, M3AAWG and its members have published dozens of prescriptive best practices implemented by industry, provided significant inputs into industry standards, and offered guidance for public policy related to the Internet, messaging and online abuse,” said Janet Jones, M3AAWG chairperson. “As increasingly sophisticated challenges to the Internet and cybersecurity emerge, we will focus the extensive expertise and experience of our members and technical advisors to collaborate on addressing the most important issues of our times. We can then provide guidance, best practices and perspectives to industry to help prevent and mitigate these issues.” “With their extensive history and deep experience in email, messaging, malware and related topics, M3AAWG members have worked tirelessly to identify and help the industry remediate and prevent the most egregious and prevalent cases of abuse,” noted Rod Rasmussen, principal at R2 Cyber, chairman of ICANN’s Security and Stability Advisory Committee and M3AAWG expert advisor. “We will carry on this work while aligning our efforts around current, emerging, and future abuse and cybersecurity challenges to ensure our members and their stakeholders continue to benefit from these collective efforts.”
M3AAWG members will meet mid-June in London to continue their collaboration efforts, with a focus on regional cybersecurity and online abuse issues. More information and member registration can be found at /upcoming-meetings and Twitter (@M3AAWG), LinkedIn, Facebook and YouTube. Session updates and more info also will be posted on the blog.
About M3AAWG
The Messaging, Malware and Mobile Anti-Abuse Working Group (M3AAWG) is where the industry comes together to work against bots, malware, spam, viruses, denial-of-service attacks and other online exploitation. M3AAWG (www.m3aawg.org) members represent more than one billion mailboxes from some of the largest network operators worldwide. It leverages the depth and experience of its global membership to tackle abuse on existing networks and new emerging services through technology, collaboration, and public policy. It also works to educate global policy makers on the technical and operational issues related to online abuse and messaging. Headquartered in San Francisco, Calif., M3AAWG is driven by market needs and supported by major network operators and messaging providers.
Contact:
PR@M3AAWG.org
Messaging, Malware and Mobile Anti-abuse Working Group Members Gather to Address Email, Messaging and Online Security and Abuse Issues
SAN FRANCISCO, Calif., Feb. 10 – The Messaging, Malware and Mobile Anti-abuse Working Group (M3AAWG) will host its 54th general meeting February 21-24, where members of the group will collaborate on messaging delivery and abuse; network and transport security; cybersecurity across devices; and relevant industry standards and policy issues.
In a deep-dive look at today’s email environment, industry experts including Todd Herr will host a panel looking at changes and challenges as well as opportunities for email. Panelists will examine adoption of authentication, spam issues, email traffic patterns, the role of governments in email security efforts, automation and predictions for 2022. Severin Walker, M3AAWG board of directors co-chair, will moderate.
M3AAWG also will announce priority and focus areas including critical messaging, transport and cybersecurity issues. Additional sessions for members will include speakers and panels addressing:
- Resource Public Key Infrastructure (RPKI): what it is, how does it work and different implementation methods
- Using computer vision to detect look-alike malicious emails
- How email service providers should adapt email collection practice in an increasingly privacy-oriented environment
- DNS-bound client identity for webhooks and API interactions
- Using computer vision to identify brand phishing messages in a large email stream
- How to evolve beyond SMS for phone number verification
- A look at the current state of open tracking in emails
- An introduction to the organization’s new Brand Protection Kit
The group also will recognize a member of the industry with its Mary Litynski lifetime achievement award.
More information and member registration can be found at /upcoming-meetings and Twitter (@M3AAWG), LinkedIn, Facebook and YouTube. Session updates and more info also will be posted on the blog.
About M3AAWG
The Messaging, Malware and Mobile Anti-Abuse Working Group (M3AAWG) is where the industry comes together to work against bots, malware, spam, viruses, denial-of-service attacks and other online exploitation. M3AAWG (www.m3aawg.org) members represent more than one billion mailboxes from some of the largest network operators worldwide. It leverages the depth and experience of its global membership to tackle abuse on existing networks and new emerging services through technology, collaboration, and public policy. It also works to educate global policy makers on the technical and operational issues related to online abuse and messaging. Headquartered in San Francisco, Calif., M3AAWG is driven by market needs and supported by major network operators and messaging providers.
Contact:
Anne Price
anne@M3AAWG.org
602-330-6495
Coalition Against Stalkerware Named J.D. Falk Award Winner for Raising Awareness About and Helping Victims of Malicious Spying Apps

Award Honors Falk, Antispam Pioneer and a M3AAWG Founding Member
