Technology Summaries
The intent of these summaries is for each to be a high-level overview, giving a few main points and some corrections to common misconceptions, and to point readers to further documentation for more detail. The idea came from seeing the common misconceptions and thinking that it would be good for M3AAWG to do some one-page summaries of relevant technologies to steer people in the right direction. They are also not meant to be comprehensive, but just to cover some key points.
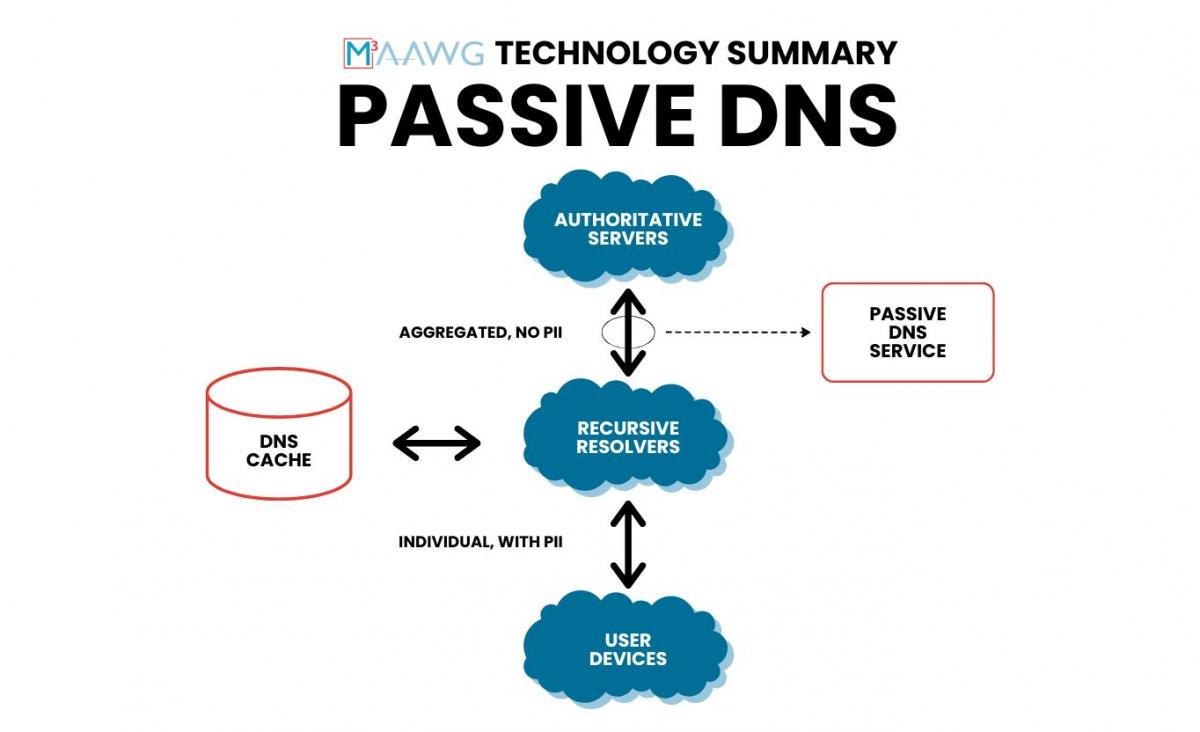
Passive DNS
The term “passive DNS” refers to the process of passively collecting successful DNS lookups and responses. It is called passive because it doesn’t involve actively probing the DNS, just logging queries and responses that are organically happening.

DMARC (Domain-based Message Authentication, Reporting, and Conformance)
DMARC is a mechanism that uses the email authentication protocols DKIM and SPF to ensure that the use of a domain in the “From” line of an email message, or the sender address, is authorized by the domain owner
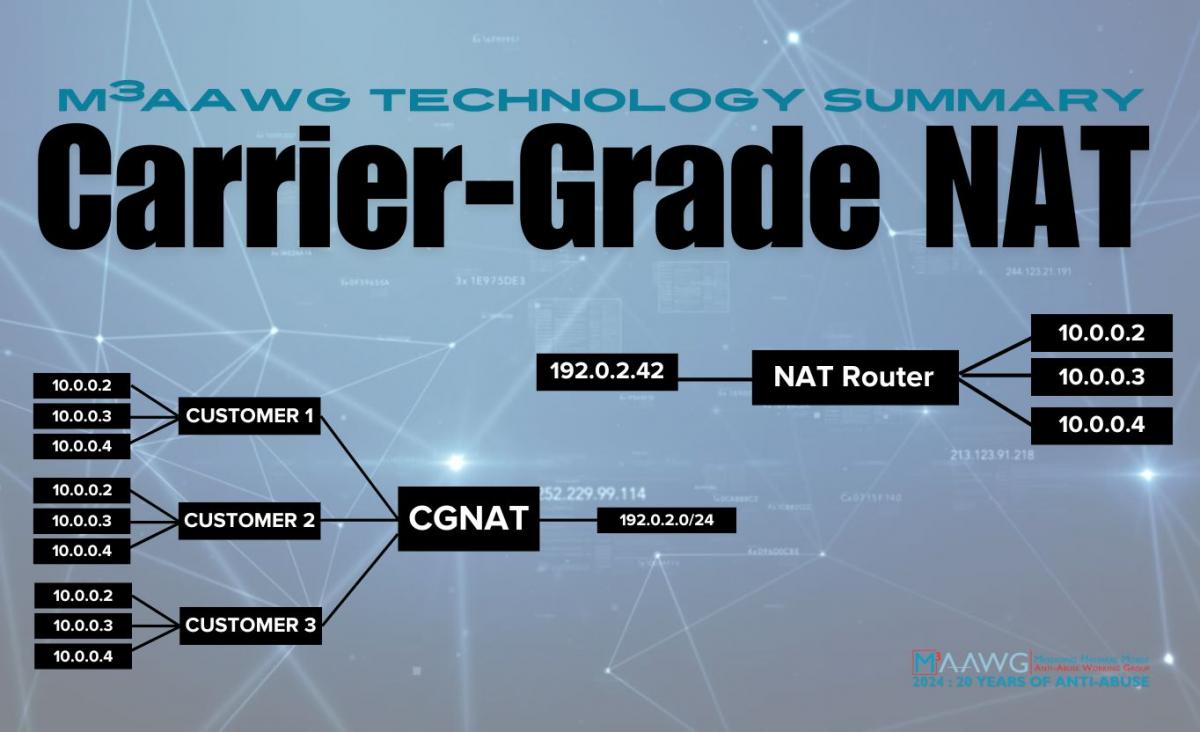
Carrier-Grade NAT
This M3AAWG Technology Summary provides clarity on what Carrier-Grade NAT is and the issues that surround it.
Sender Policy Framework (SPF)
SPF is an email authentication protocol that checks which IP addresses are authorized to send mail on behalf of the originating domain.
Domain Keys Identified Mail (DKIM)
DKIM is an email authentication protocol that creates an association between a domain and the messages it sends using digital signatures. A sequence of messages signed with the same domain name is assumed to provide a reliable base of information about mail associated with the domain name’s owner, which may feed into an evaluation of the domain’s reputation.

Email Authentication
Email authentication involves one or more technical processes used by sending and receiving mail systems to verify the email originated with an authorized domain name server and is received in a valid format. Email authentication creates signals about the mail that can be used in spam filtering and other mail handling decisions, and may even point to fraudulent senders.
